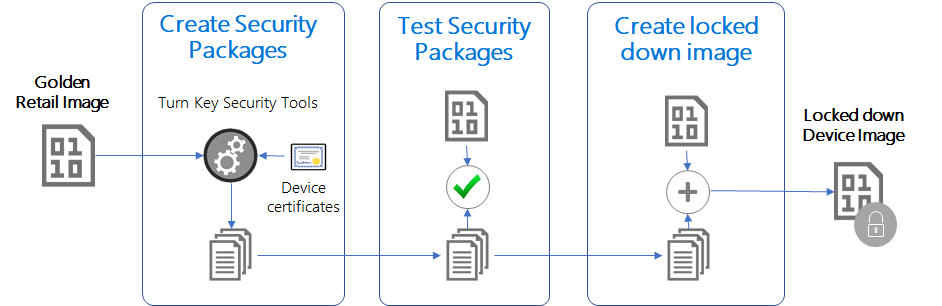
Enabling Secure Boot, BitLocker, and Device Guard on Windows 10 IoT Core - Windows IoT | Microsoft Learn
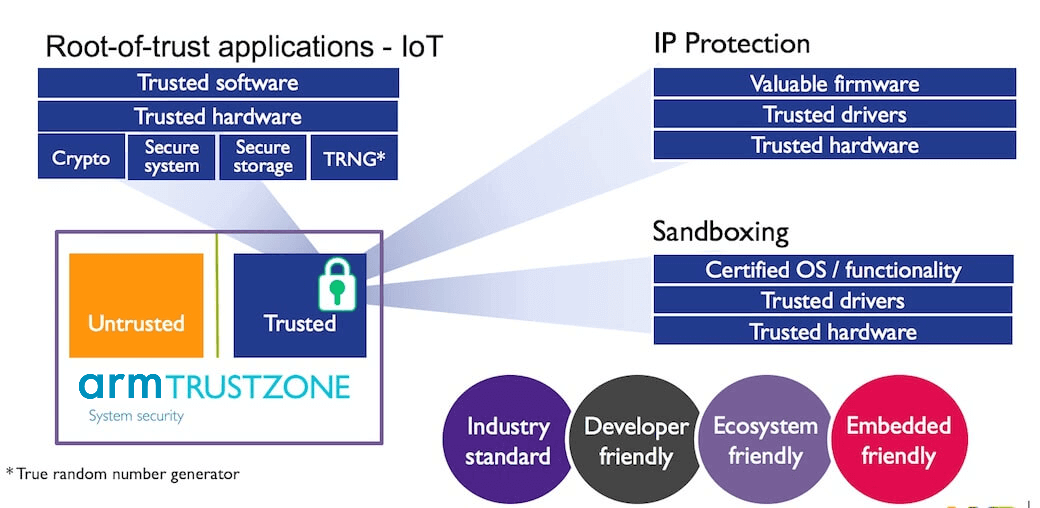
Designing secure embedded IoT devices - Architectures and Processors blog - Arm Community blogs - Arm Community

Build highly secure IOT device: secure boot, measured boot and attestation, secure storage etc | by lei zhou | Medium